The certificate authority system represents a silent cartel that has monopolized digital trust through root store control, compliance capture, and economic barriers to entry.
The CA system is not decentralized trust. It is permissioned encryption.
THE DECENTRALIZATION ILLUSION
Certificate authorities market themselves as independent trust validators. Documentation emphasizes cryptographic protocols, audit compliance, and technical standards. These formalisms create the appearance of distributed verification.
The reality operates differently. The CA system has consolidated through regulatory capture and economic consolidation. Root store inclusion determines commercial viability. Browser trust decisions determine market survival. The system presents as decentralized while operating as an oligopoly.
This arrangement functions as trust centralization: encryption that requires permission from a cartel of approved authorities.
CARTEL CONTROL ARCHITECTURE
The certificate authority cartel maintains monopoly control through four interconnected mechanisms:
Each mechanism reinforces cartel control. Root store control determines market access. Regulatory capture determines operational compliance. Economic consolidation determines competitive viability. Sovereignty exclusion determines geopolitical alignment.
THE PERMISSIONED LAYER: ENCRYPTION AS CARTEL SERVICE
The CA system initially presents as public key infrastructure. It emphasizes cryptographic security, identity verification, and chain of trust. This phase follows the logic of technical standardization—creating interoperable security protocols.
The permissioned phase emerges at scale. The system transforms from technical infrastructure to cartel service. Trust decisions become commercial decisions. Compliance requirements become market barriers. The CA/Browser Forum becomes the cartel's regulatory body.
The technical justification—security standards, audit compliance, fraud prevention—serves as operational cover for monopoly control. The certificate becomes the cartel's permission slip.
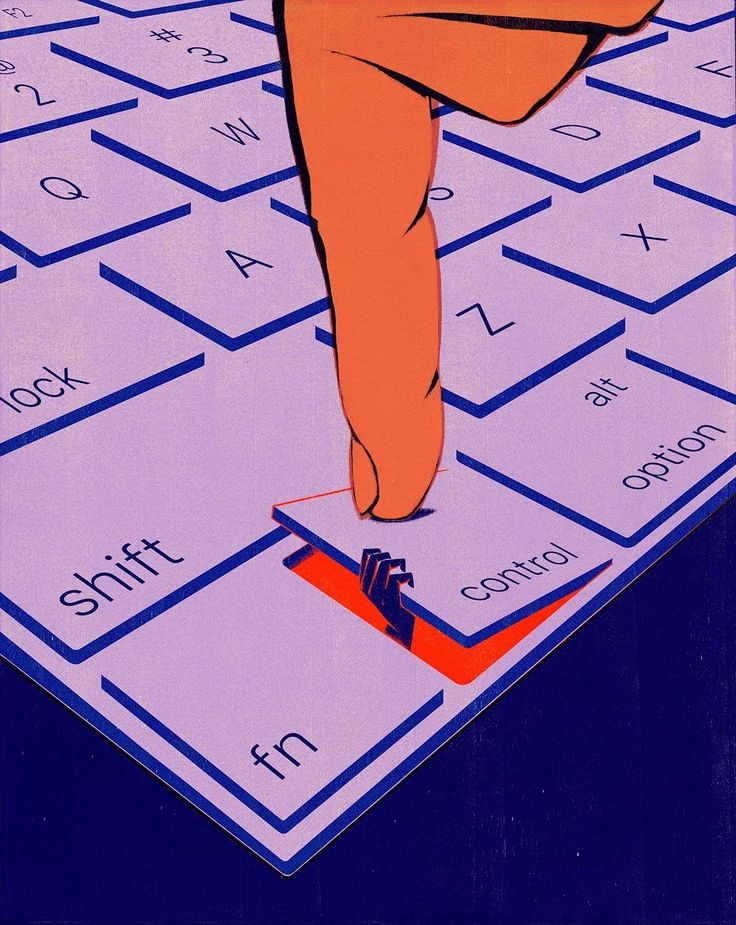
Modern encryption does not require breaking cryptography. It requires controlling who can issue valid certificates.
MONOPOLIZATION MATRIX: HOW THE CARTEL OPERATES
The certificate authority cartel functions through specialized division of control:
Each cartel member specializes in specific control vectors while collectively excluding new entrants.
TRUST FLOW ANALYSIS: HOW PERMISSION PROPAGATES
The certificate authority system follows a predictable permission flow:
The flow is unidirectional: sovereignty determines economics, economics determines technology, technology enables enforcement.
FAILURE CASCADE: WHEN THE CARTEL BREAKS
The certificate authority system creates systemic fragility through centralization:
Each failure strengthens the cartel by eliminating weaker members and increasing dependency on survivors.
LET'S ENCRYPT: CARTEL CO-OPTATION STRATEGY
THE DISRUPTION ILLUSION
Let's Encrypt presented as a revolutionary alternative: automated, free certificates challenging the commercial CA model. The reality operates differently. Let's Encrypt functions as cartel pressure relief valve and surveillance enhancement tool.
CARTEL INTEGRATION MECHANISMS
1. Root store dependency: Relies on IdenTrust cross-signature, remaining within established trust hierarchy
2. Compliance adherence: Follows CA/B Forum Baseline Requirements, reinforcing cartel regulatory framework
3. CT log integration: Feeds all certificates into Certificate Transparency logs, enhancing state surveillance capabilities
4. Rate limiting as control: Artificial issuance limits prevent true mass-scale alternative trust deployment
THE SURVEILLANCE FUNCTION
Let's Encrypt's automation creates perfect surveillance conditions: every certificate issued is automatically logged in CT, creating real-time map of internet domain relationships. The service appears disruptive while actually enhancing cartel control capabilities.
Let's Encrypt does not break the cartel. It modernizes it.
DIAGNOSTIC FRAMEWORK
To measure trust centralization in any encryption system, evaluate four diagnostic dimensions:
Systems scoring high across all four dimensions have transformed encryption into cartel-controlled permission system.
TRUST SOVEREIGNTY ARCHITECTURE
Current certificate infrastructure follows cartel convenience logic. Alternative models exist in cryptographic history. The Web of Trust demonstrates peer-to-peer verification without centralized authorities. Blockchain-based identity systems show decentralized consensus for credential validation.
Trust sovereignty requires architectural independence from initial design:
Decentralized root distribution: Implement peer-to-peer root certificate distribution outside vendor control.
Multiple trust anchors: Require certificates to be validated by multiple independent authorities.
Transparent validation algorithms: Make trust decisions algorithmically verifiable rather than politically determined.
Sovereign root programs: Develop regional root stores independent of Silicon Valley corporate control.
Revocation decentralization: Implement distributed revocation mechanisms resistant to single-point takedown.
Alternative trust metrics: Develop reputation systems beyond CA issuance for domain validation.
These practices trade cartel convenience for trust sovereignty. They reject permissioned encryption in favor of verifiable cryptographic trust.
THE PERMISSION TRAP CYCLE
The certificate authority cartel follows a predictable permission escalation pattern:
1. Initial standardization: Technical standards established with corporate participation. Trust appears decentralized.
2. Regulatory capture: Large players dominate standards bodies. Compliance requirements favor established entities.
3. Economic consolidation: Market forces eliminate small players. Remaining CAs form pricing and policy coordination.
4. State collaboration: CAs establish cross-certification with governments. Surveillance capabilities embedded.
5. Cartel formalization: Industry forum becomes de facto regulatory body. New entrants effectively prohibited.
6. Sovereignty elimination: Alternative trust systems criminalized or technically excluded. Encryption requires cartel permission.
The cycle completes when digital trust becomes impossible without cartel approval.
SYSTEM NOTES
The most secure encryption is worthless when trust requires permission from those you cannot trust.