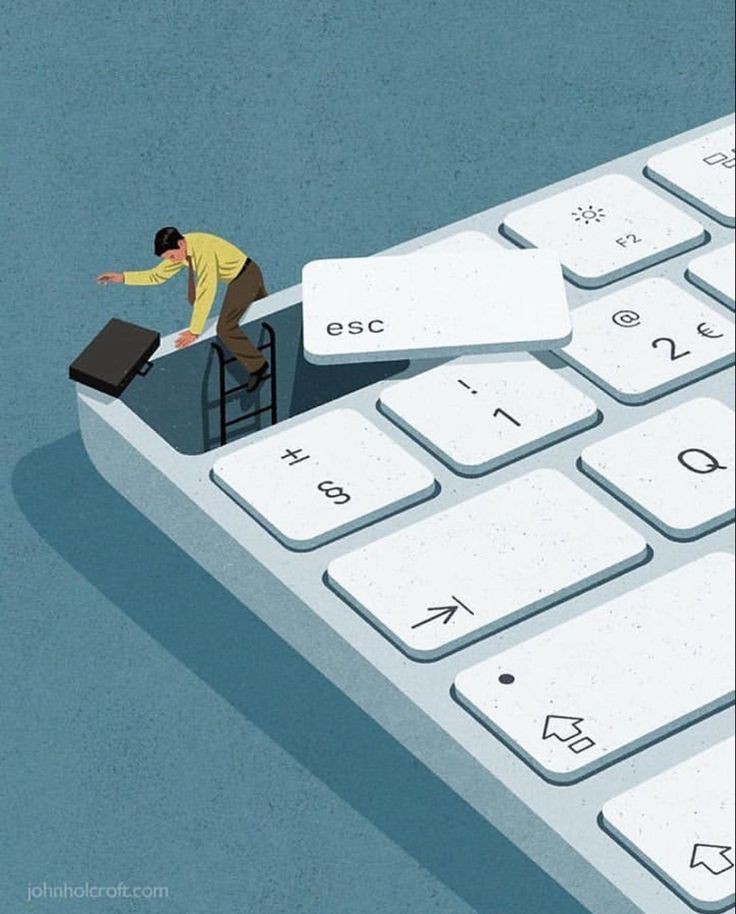
The adoption of platform-as-a-service infrastructure represents institutional dependency architecture. The exit strategy becomes impossible not through contractual obligation, but through layered technical and operational entanglement.
The cloud is not a location. It is a governance system.
THE SOVEREIGNTY ILLUSION
Public cloud platforms market themselves as neutral infrastructure providers. Documentation emphasizes portability, open standards, and migration tooling. These formalisms create the appearance of organizational autonomy.
The reality operates differently. Cloud platforms architect dependency through layered entanglement. Each layer—technical, operational, knowledge, economic—creates incremental lock-in. No single dependency prevents exit. Their cumulative weight renders migration institutionally infeasible.
This arrangement functions as architectural governance: control exercised not through prohibition, but through structural entanglement that makes alternatives nonviable.
DEPENDENCY ARCHITECTURE
Cloud platforms construct lock-in through four interdependent layers:
Each layer reinforces the others. Technical choices necessitate operational patterns. Operational patterns generate knowledge dependencies. Knowledge dependencies obscure economic alternatives. The system self-stabilizes.
THE GOVERNANCE LAYER: INFRASTRUCTURE AS POLITICS
Cloud platforms initially present during adoption phases as utility providers. They emphasize cost reduction, scalability, and operational simplicity. This phase follows the logic of infrastructure abstraction—removing complexity through managed services.
The governance phase emerges gradually. Platform control expands from infrastructure provisioning to application architecture decisions. Managed services replace open-source components. Platform-specific implementations become default choices. The vendor's roadmap dictates organizational technical direction.
The technical justification—developer productivity, operational efficiency, security best practices—serves as operational cover for governance capture. The platform becomes the institutional operating system.
Cloud sovereignty is not measured by data location. It is measured by architectural optionality.
EXIT MATRIX: MIGRATION DIMENSIONS
Cloud exit strategies exist across three dimensions:
Most organizations evaluate only technical viability. Institutional cost—knowledge retraining, operational redesign, economic renegotiation—determines actual feasibility.
VENDOR PATTERNS
AWS: THE COMPREHENSIVE OPERATING SYSTEM
AWS constructs dependency through service breadth. The platform offers managed alternatives for every infrastructure component. Each service features proprietary APIs, custom authentication, and unique operational models. Exit requires not migration, but ecosystem reconstruction.
AZURE: THE ENTERPRISE INTEGRATION LAYER
Azure builds dependency through enterprise integration. The platform connects directory services, compliance frameworks, and legacy systems. Exit disrupts not just applications, but organizational identity and compliance verification systems.
GOOGLE CLOUD: THE DATA GRAVITY WELL
Google Cloud architects dependency through data services. BigQuery, Bigtable, and Spanner create proprietary data formats and query languages. Data egress costs and transformation complexity create gravitational lock-in.
Each pattern achieves the same outcome through different architectural vectors: reduced optionality.
DIAGNOSTIC FRAMEWORK
To measure cloud dependency in any organization, evaluate four diagnostic dimensions:
Organizations scoring high across all four dimensions have transformed technical infrastructure into institutional governance.
SOVEREIGNTY DESIGN PRINCIPLES
Current cloud adoption follows vendor optimization logic. Alternative models exist in infrastructure design history. The UNIX philosophy of small, composable tools demonstrates modularity at scale. Internet protocol design emphasizes interoperability over optimization.
Cloud sovereignty requires architectural discipline from initial adoption:
Abstraction layers: Maintain separation between business logic and platform implementations.
Open standards prioritization: Prefer services with compatible alternatives across providers.
Data portability enforcement: Architect data formats and access patterns for multi-cloud operation.
Knowledge diversification: Maintain expertise across multiple platforms and on-premises alternatives.
Exit strategy budgeting: Allocate resources for periodic migration feasibility testing.
These practices trade short-term optimization for long-term optionality. They reject vendor abstraction in favor of architectural sovereignty.
SYSTEM NOTES
Infrastructure becomes governance when exit transforms from technical migration to institutional reconstruction.